Identity Verification
For most agreements, a secure signing link delivered to the recipient's inbox is sufficient. But for higher-stakes documents, financial agreements, regulated transactions, legal contracts, you can require recipients to complete an additional identity check before they can access the document.
You configure this per recipient, so you can apply different levels of verification to different people in the same agreement.
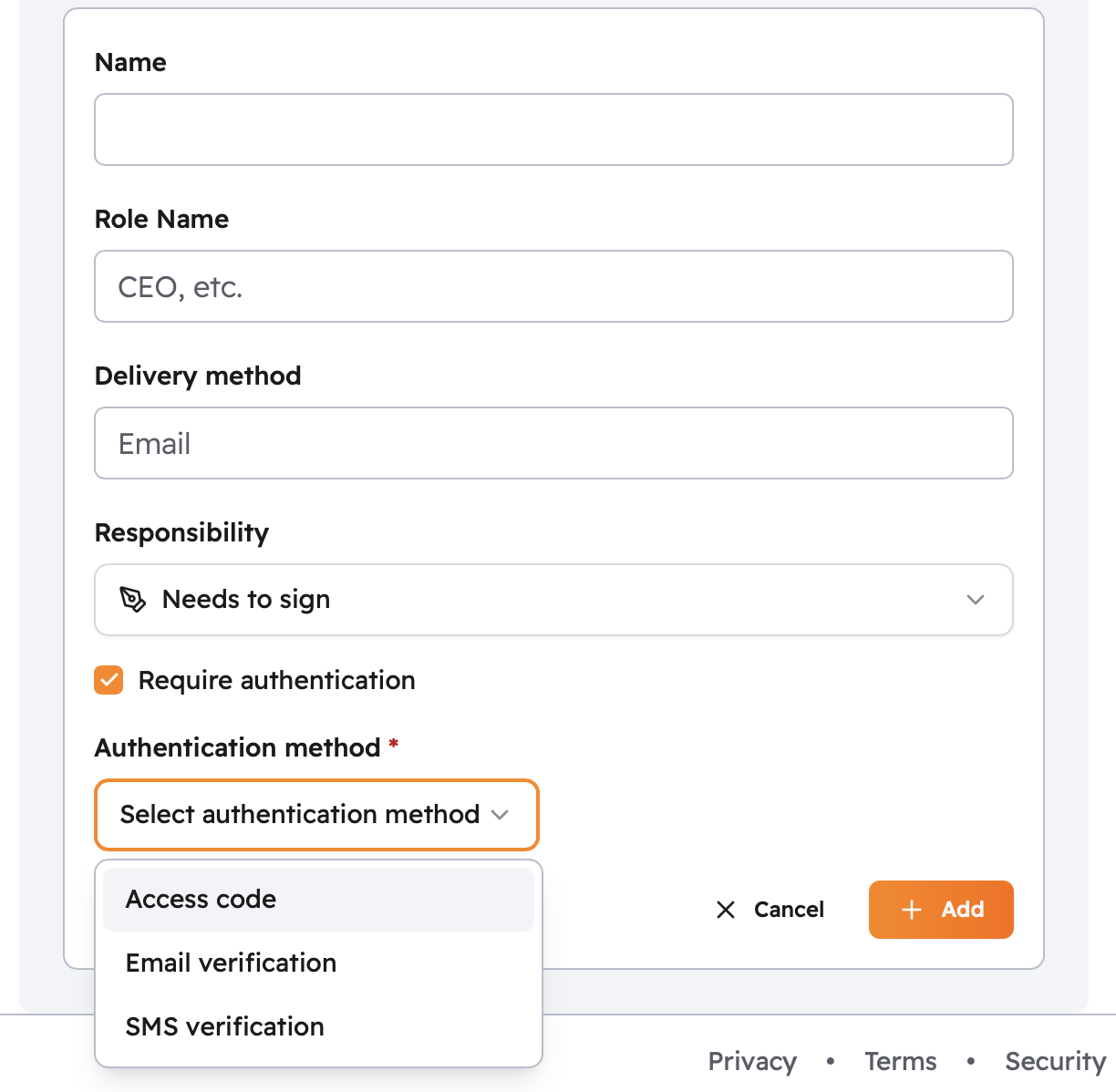
Verification Methods
| Method | How it works | When to use it |
|---|---|---|
| None (default) | Recipient accesses the document via the unique link in their email | Standard business documents, internal agreements, low-risk transactions |
| Email code | A one-time code is sent to the recipient's email; they enter it before signing | When you want to confirm the recipient has active access to their inbox at the time of signing |
| SMS code | A one-time code is sent to the recipient's phone via text | Financial, healthcare, or real estate transactions where an extra layer of assurance is needed |
| Access code | You set a code and share it with the recipient separately (e.g., by phone) | When you want verification to travel through a different channel than the signing link |
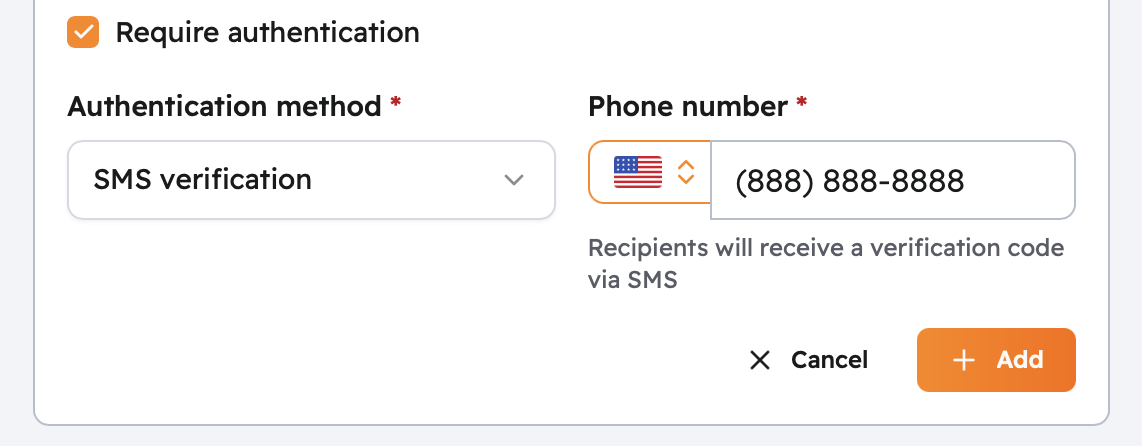
Setting Up SMS Verification
SMS verification requires the recipient's mobile number when you add them.
- Select SMS as the verification method when adding the recipient.
- Enter their mobile number with country code.
When they click the signing link, a 6-digit code is sent to their phone. They enter the code to access the document.
Setting Up an Access Code
An access code is a passphrase you create and share with the recipient through a separate channel, by phone, in person, or through another communication method outside of email.
- Select Access Code when adding the recipient.
- Enter a code (6–10 characters recommended).
- Share the code with the recipient through a channel separate from the signing invitation.
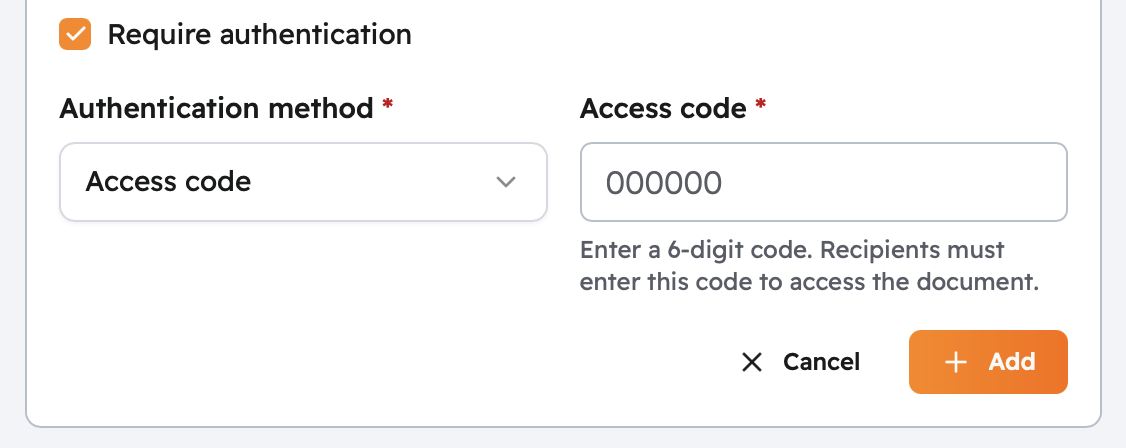
Tips:
- Use a code that isn't easy to guess, avoid birthdays or simple number sequences
- Share the code through a different channel than the signing email
- Use a unique code per recipient if multiple signers are on the same agreement
Repeated incorrect attempts will temporarily lock the recipient out of the document.
Related Topics
- Recipients: add recipients and assign roles
- Signing Experience: what recipients see when they sign
- Audit Trail: authentication events are recorded in the agreement's audit record